Immadi Ravi Arrest: iBomma Piracy Tactics Exposed | Telugu Film Losses
Satellite Feed Hacking Details
Satellite feed hacking, as uncovered in the Immadi Ravi/iBomma investigation, is a stealthy piracy tactic where criminals intercept unencrypted or weakly protected satellite TV broadcasts to capture high quality video streams of movies and shows before they hit theaters or OTT platforms. This method was one of Ravi’s “coordinated acquisition pipelines,” blending low-tech scouting with high-tech breaches, and allowed his network to leak films like Kantara and Game Changer within hours of broadcast. Based on police probes and industry reports from the November 17, 2025, briefing, here’s a breakdown of how it worked in Ravi’s operation, plus broader technical insights:
How Ravi’s Network Executed Satellite Feed Hacking
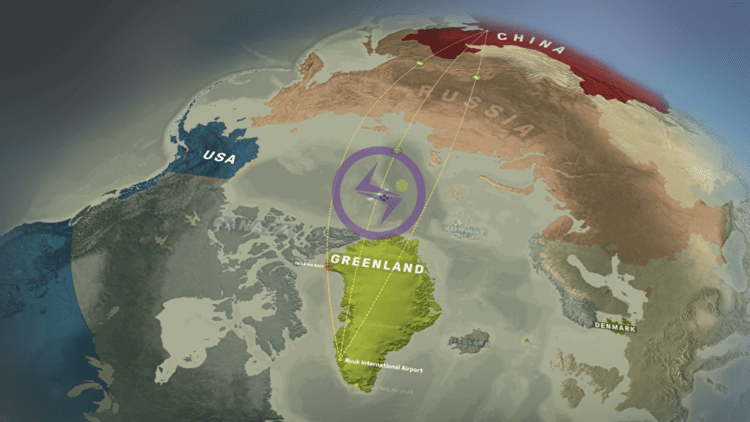
- The Setup and Coordination: Ravi’s overseas team (in the Netherlands, Switzerland, and Myanmar) scouted broadcast schedules from TV networks like Gemini TV or Zee Telugu, which air premieres via satellite (e.g., on Intelsat or AsiaSat birds). Camcorders in Indian theaters (like arrested operative Jana Kiran Kumar) provided ground-truth backups, but satellites were the premium source for pristine HD rips. The process was “coordinated”: Local spotters in Hyderabad/Dubai relayed air dates, triggering remote hacks.
- Technical Breach Mechanics:
- Signal Interception: Using affordable Ku-band satellite dishes (₹5,000-10,000) and LNB (Low Noise Block) converters, hackers tuned into C/Ku-band frequencies broadcasting unencrypted MPEG-2/4 streams. Ravi’s crew exploited “test feeds” or pre-encryption windows gaps where content is sent raw from studios to uplink stations (e.g., in Mumbai or Chennai). Tools like professional-grade DVB-S2 receivers (e.g., modified Dreambox or Vu+ decoders) captured the feed in real-time, dumping it as TS (Transport Stream) files.
- Decryption Cracks: If encrypted (via CAS like Irdeto or Conax), they deployed illegal “card-sharing” servers or cloned smart cards bought on dark web forums for ₹1,000-5,000. Ravi’s DRM-hacking skills (honed from ER Infotech) extended here, using software like OSCam or CCCam to emulate legitimate decoders remotely over VPNs, bypassing geo-fences.
- Processing and Upload: Captured feeds were demuxed (separated audio/video) with tools like FFmpeg on seized laptops, then re-encoded to H.264/H.265 for web streaming. Within 2-4 hours, files hit offshore Amsterdam servers via encrypted FTP, ready for iBomma/Bappam mirrors. This beat theater camcording’s shaky quality, fetching premium dark web sales (₹50,000-2 lakh per title).
- Scale and Evasion in Ravi’s Op: Over 21,000 films archived on 200+ hard disks included satellite-sourced classics and 2025 hits. To dodge detection, feeds were relayed through decoy proxies in the Caribbean (tied to Ravi’s St. Kitts citizenship), with metadata stripped using ExifTool. Police traced this via server logs seized post-arrest, revealing ties to broadcast piracy rings in Southeast Asia.
Broader Context and Risks
- Why It’s Effective for Piracy: Satellites cover vast areas cheaply (no physical access needed), ideal for global ops like Ravi’s. It’s cheaper than OTT hacks but riskier signals are line-of-sight, so urban setups in Hyderabad/Dubai were key. Industry losses: ₹3,700 crore to Telugu/Tamil cinema in 2024 alone from such leaks. timesofindia.indiatimes.com
- Legal/Tech Countermeasures: Under India’s Copyright Act and IT Rules, it’s punishable by 3-7 years jail. Broadcasters now use end-to-end encryption (e.g., VideoGuard) and watermarking, but gaps persist. Police recommend AI-monitored spectrum analysis to detect rogue receivers.
This tactic highlights piracy’s evolution Ravi turned broadcast tech against itself, but his over-reliance on it left digital breadcrumbs for the cyber cops.